CrowdStrike 2026 Global Threat Report: The definitive threat intelligence report for the AI era Download report
×
![]()
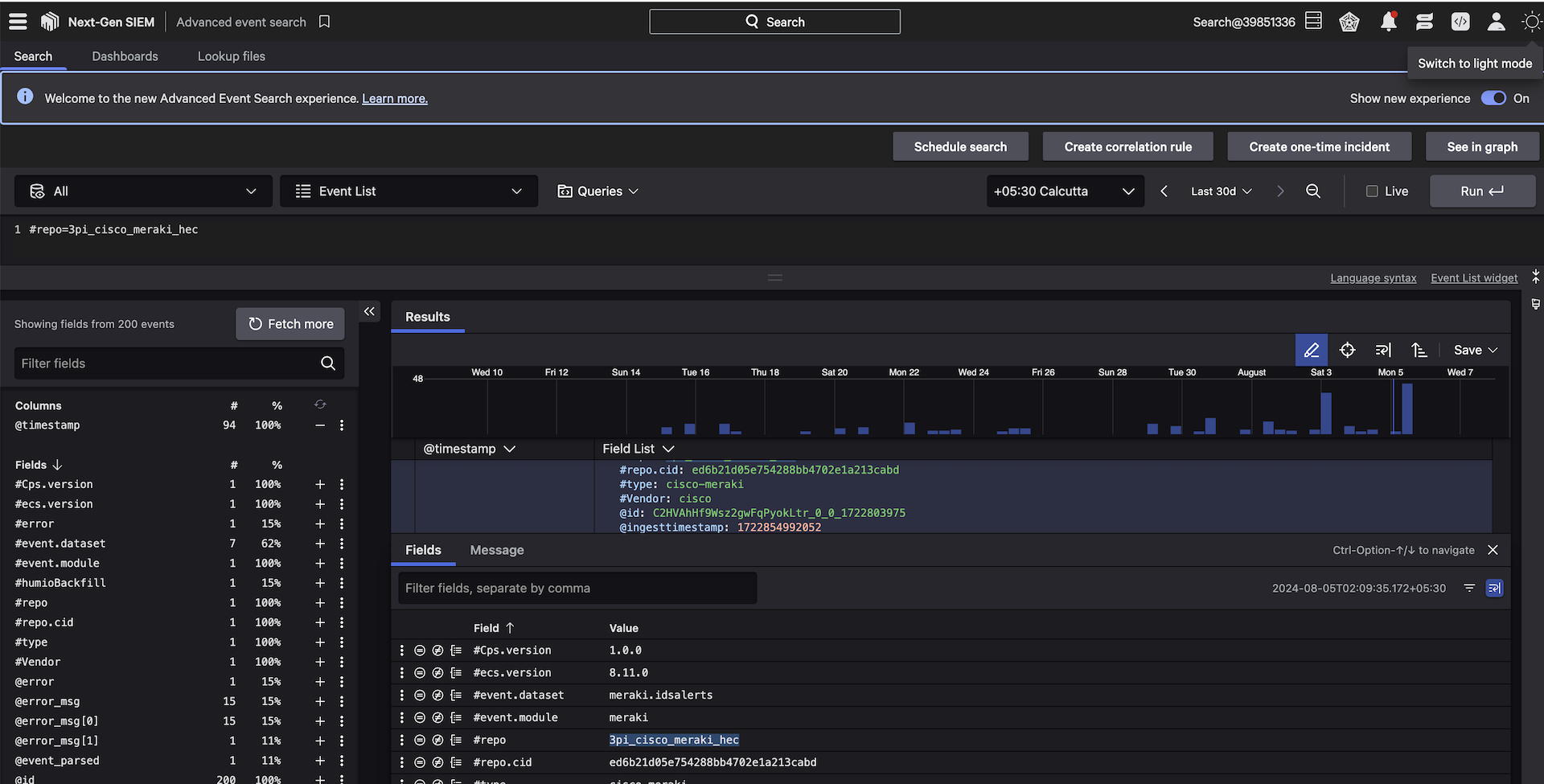
Minimize risk with unified visibility of Cisco Meraki events
Secure access proactively and gain unified visibility by easily ingesting Cisco Meraki wireless network logs into the CrowdStrike Falcon® platform. By centralizing and correlating logs and security events from Cisco Meraki, CrowdStrike, and additional third parties within CrowdStrike Falcon® Next-Gen SIEM, your team gains enhanced vulnerability detection, streamlined incident response, and an optimized security posture to ultimately protect against evolving cyber threats.
- Mitigate configuration risk
Unify visibility of access logs and security events by storing and analyzing Cisco Meraki data alongside other security telemetry within the Falcon platform - Streamline investigations and incident response
Accelerate response with detailed timelines of events and actionable forensic data from Cisco Meraki logs, such as unauthorized access and configuration changes, using built-in search and filtering capabilities from Falcon Next-Gen SIEM - Improve threat hunting
Store and correlate your security data with other data sources leveraging the Falcon platform as a destination, including real-time detections and blazing-fast search to rapidly shut down threats
Get Started
Easily ingest Cisco Meraki logs into the Falcon platform
- Mitigate configuration risk
- Streamline investigations and incident response
- Improve threat hunting
Not A CrowdStrike Customer?
Try CrowdStrike


.png)


