- 01
- 02
- 03
- 04
- 05
- 06
- 07
- 08
- 09
Zero Trust authorization policies
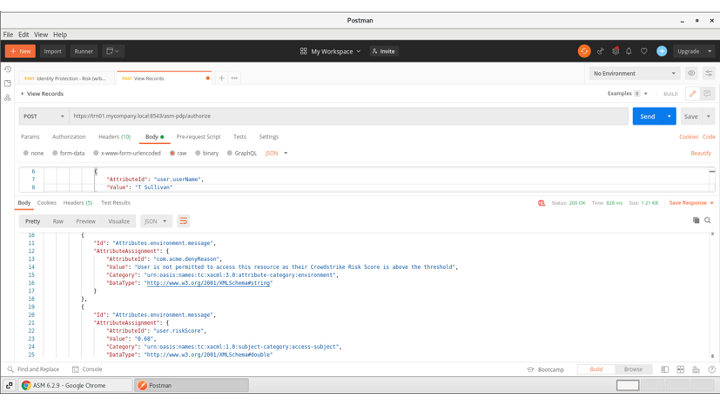
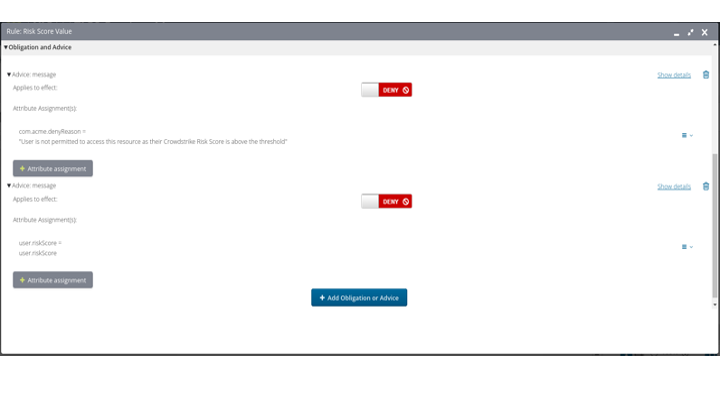
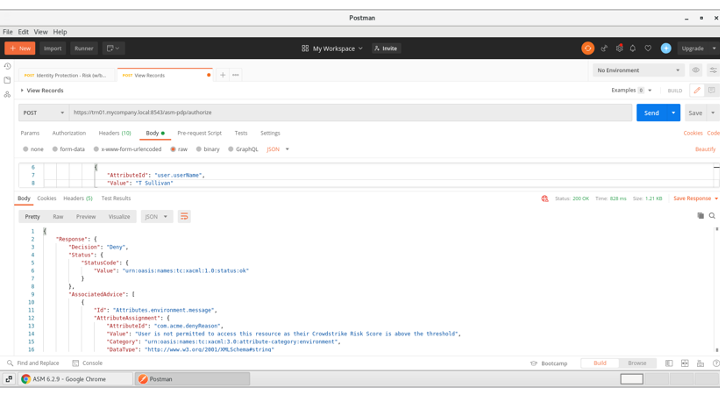
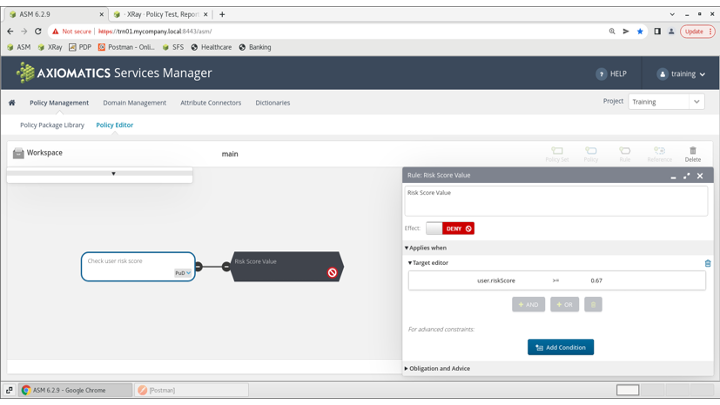
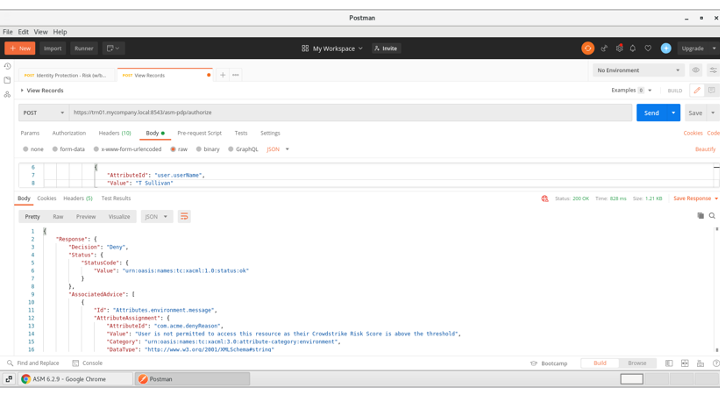
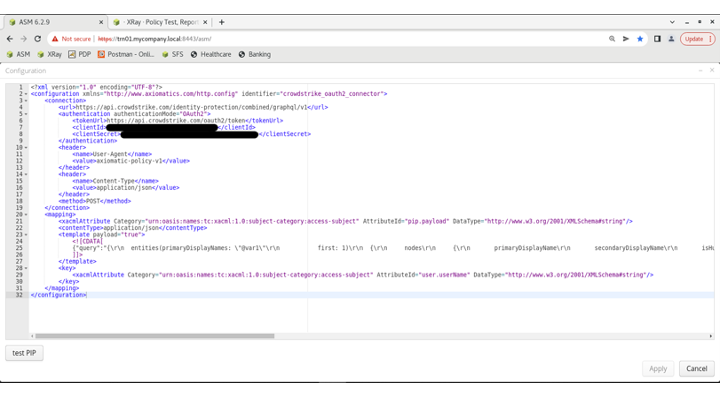
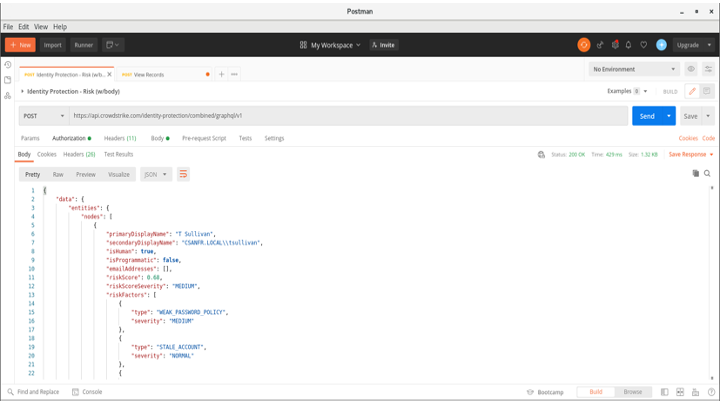
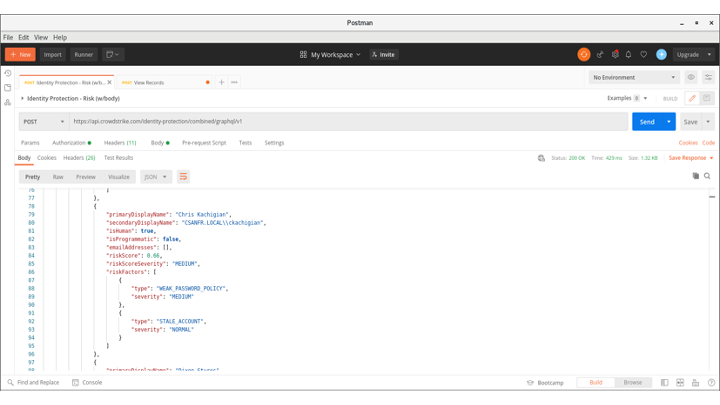
Axiomatics‘ authorization solution uses attribute-based access control (ABAC) to address enterprise application access challenges across on-premises, cloud or hybrid infrastructures. It allows for enterprise-wide rollout of ABAC, enabling organizations to manage access based on corporate access policies. Access decisions are made in real-time to ensure critical corporate applications, data and processes are only accessed in adherence to corporate policies that specify what a user has access to, how much access they have, when they get access and under what conditions. By integrating with the CrowdStrike Falcon® platform, Axiomatics empowers organizations to connect risk scores derived from Falcon Zero Trust Assessment (ZTA) to enact real-time authorization decisions across the entire application stack including micro services, APIs and API gateways.
- Enable zero trust
Build risk-based decision making into an enterprise authorization strategy to support a Zero Trust strategy. - Get threat context
Leverage context from the CrowdStrike Falcon platform‘s enriched security data to balance security and productivity with fine-grained policy decisions to apply the right decisions at the right time. - Achieve comprehensive control
Extend security controls from endpoint(s) to enterprise resources (e.g. applications, micro services, APIs, data) to ensure consistent policy execution.
Get Started
Zero Trust authorization policies
- Enable zero trust
- Get threat context
- Achieve comprehensive control
Not A CrowdStrike Customer?
Try CrowdStrikeDetails
Built by
AxiomaticsCategories
Cloud Security Identity SecurityRequirements
Falcon Insight XDR Falcon Identity Protection



