- 01
- 02
- 03
- 04
- 05
- 06
Easy NAC agentless Network Access Control to verify endpoint compliance
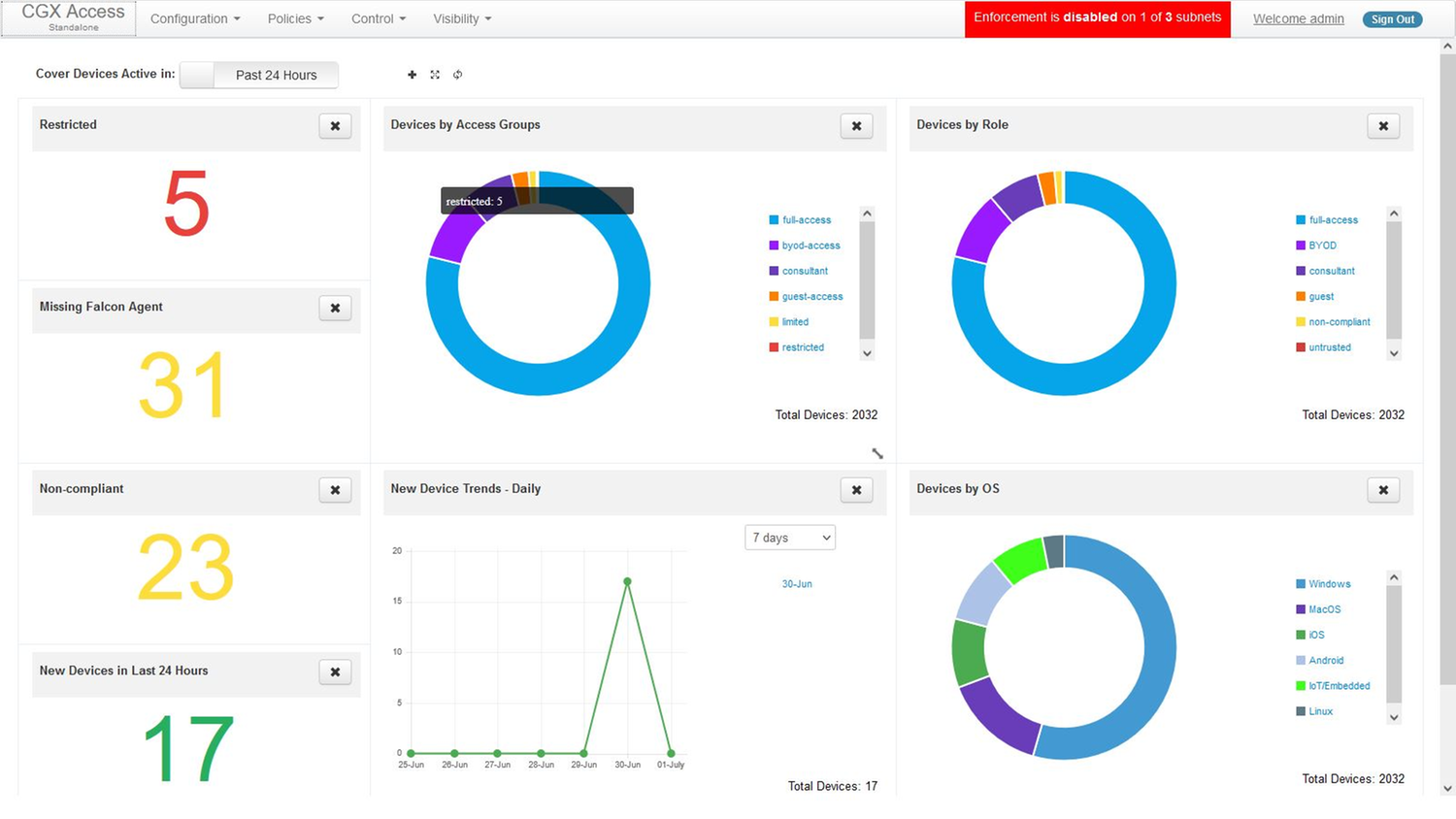
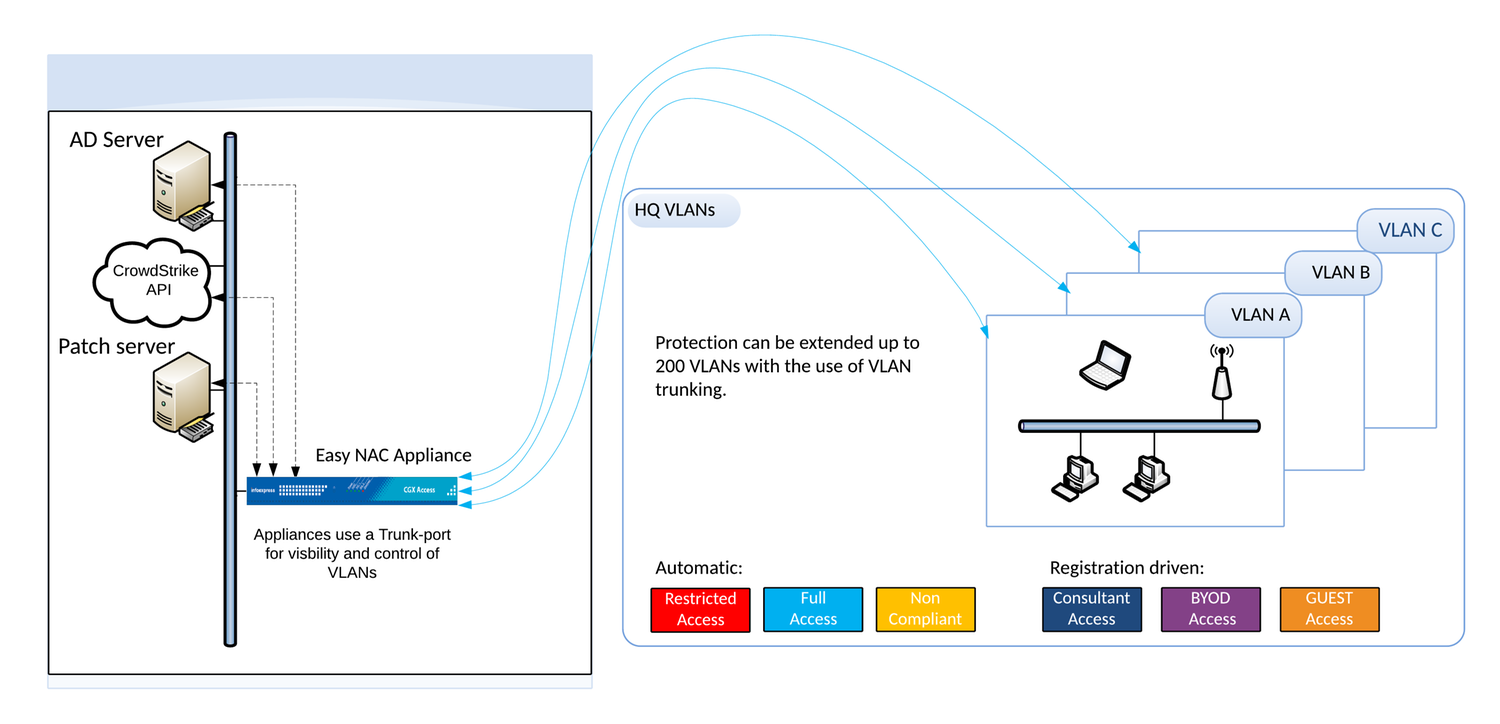
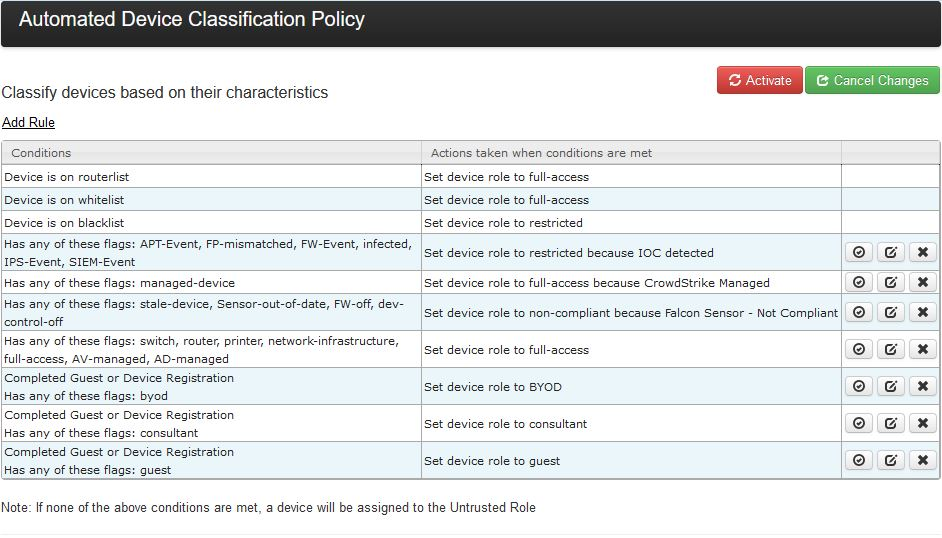
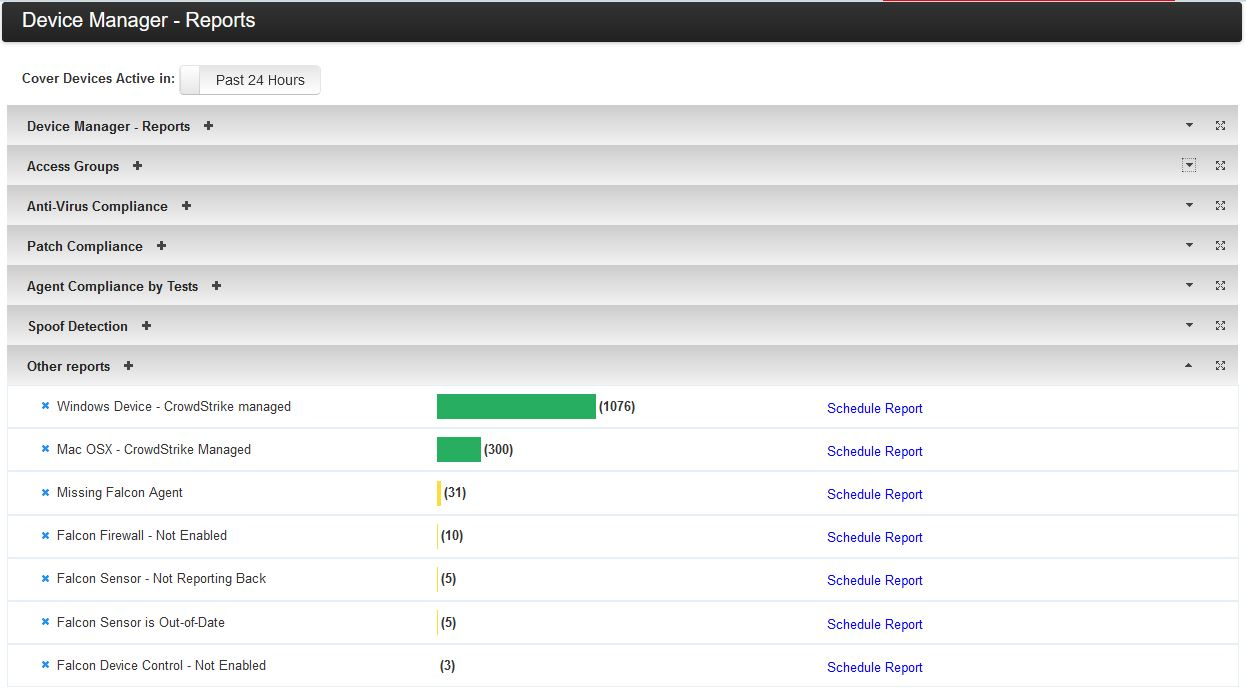
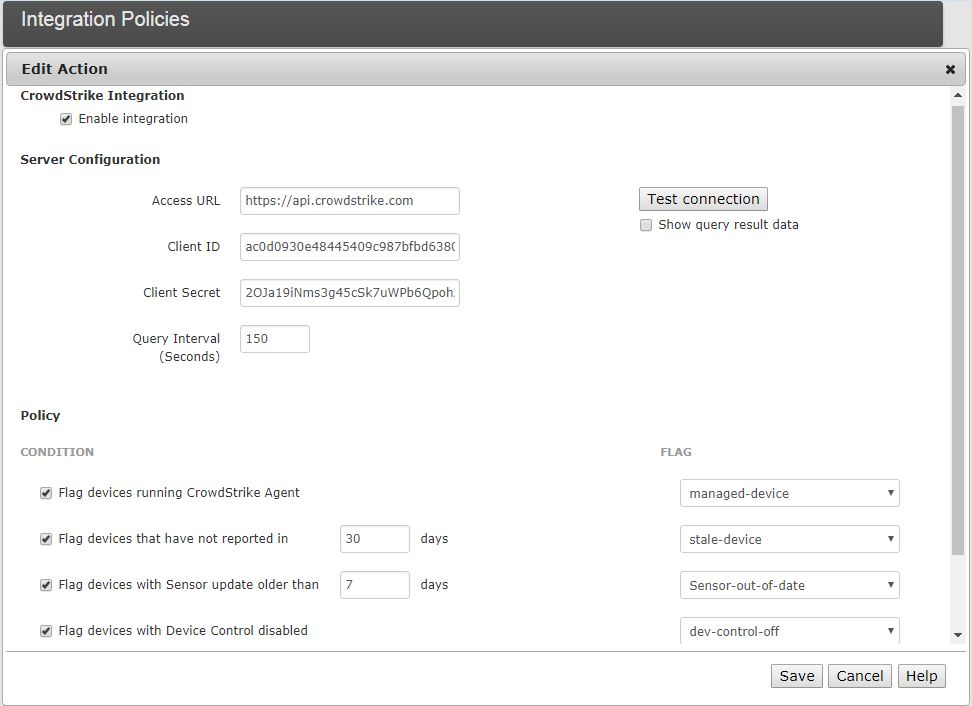
The Easy NAC solution provides a Zero Trust solution, where devices are restricted at the point of access, and only compliant devices are allowed network access. By Integrating with the CrowdStrike Falcon® platform, Easy NAC solution can automatically learn what devices should be trusted and quarantine untrusted devices. This integration provides you with confidence that all of your corporate end-user devices are enrolled and the agents are working properly. Devices not enrolled can be restricted until enrolled. Compliance checks can be done that the sensor is up to date, Firewall enabled, and Device Control is enabled.
- Agentless Compliance Checks
Easy NAC integrates with CrowdStrike and patch management solutions to enable compliance checks with no added agents. - No Network Changes
Easy NAC is easy to deploy without network refresh delays by using ARP enforcement. ARP enforcement doesn‘t require any network changes and provides immediate detection and response. It can be deployed very quickly, and works with any brand of switch, managed or unmanaged. Instead of blocked ports or quarantine VLANs, ACLs are used for a simpler and more granular (secure) enforcement method.
Easy NAC can protect the internal network from threats by immediately restricting the offending device so it would be unable to send traffic to other devices on or off the local subnet. Easy NAC can receive event-based syslog messages or e-mail alerts from any type for security devices and take immediate action to quarantine the offending device. No special versions or APIs required, just an e-mail will do.
Get Started
Simple & secure Network Access Control (NAC)
- Agentless Compliance Checks
- No Network Changes
Not A CrowdStrike Customer?
Try CrowdStrikeDetails
Built by
InfoExpress Inc.Categories
Network and Infrastructure Security IoT SecurityRequirements
Falcon Insight XDR Falcon PreventSupport





