CrowdStrike 2026 Global Threat Report: The definitive threat intelligence report for the AI era Download report
×
![]()
×
![]()
×
![]()
- 01
- 02
- 03
Empower your SOC
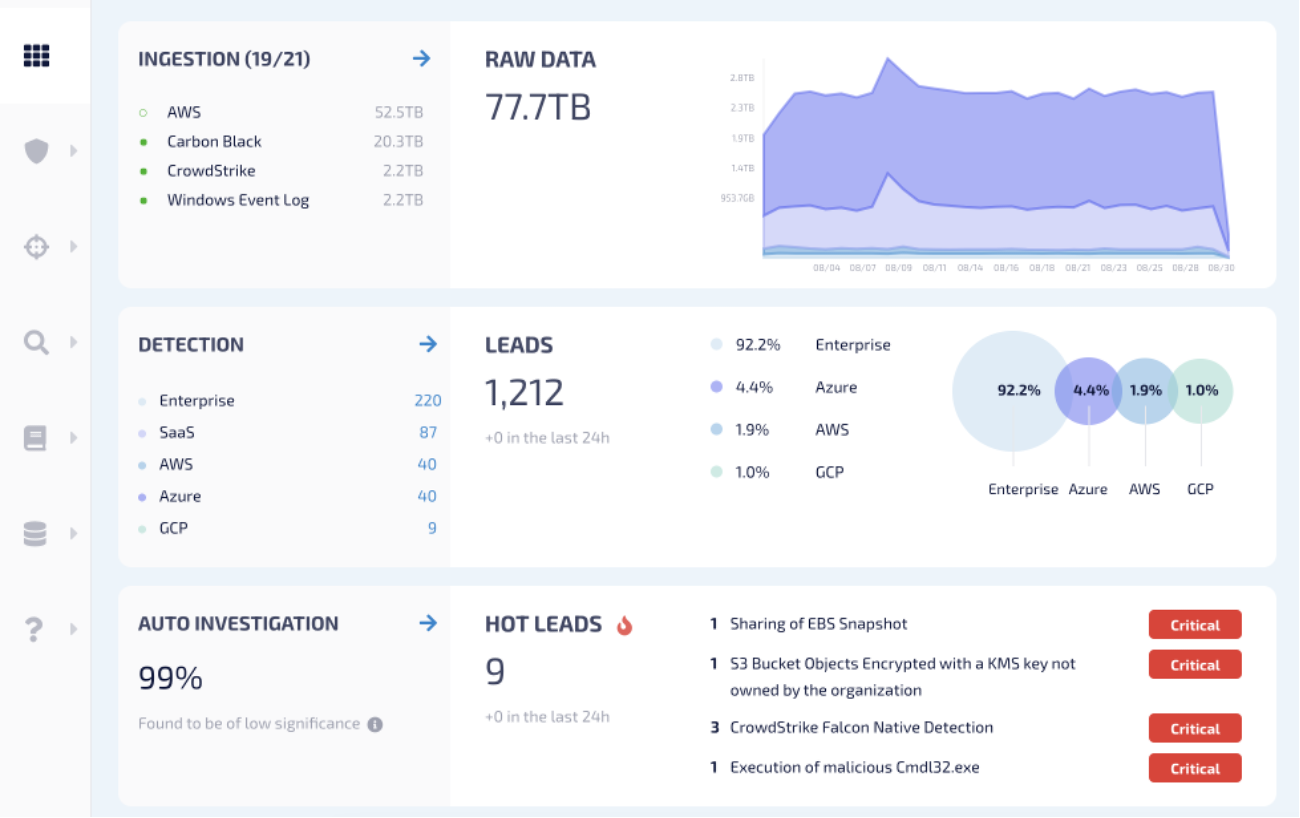
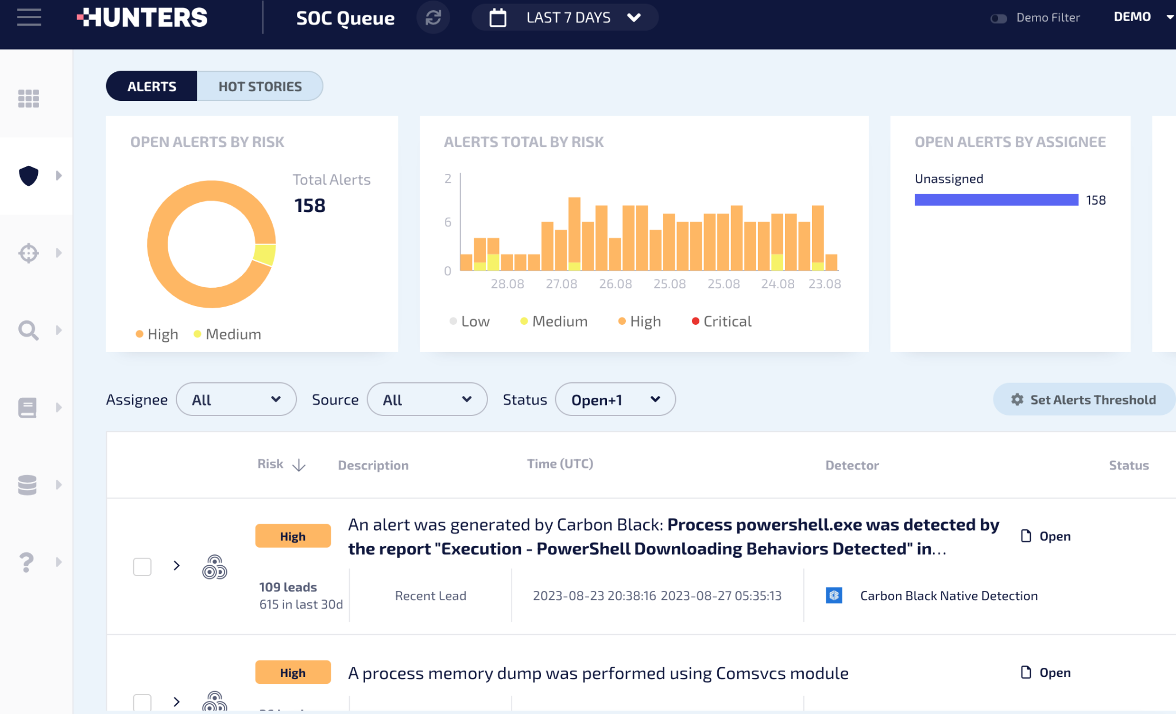
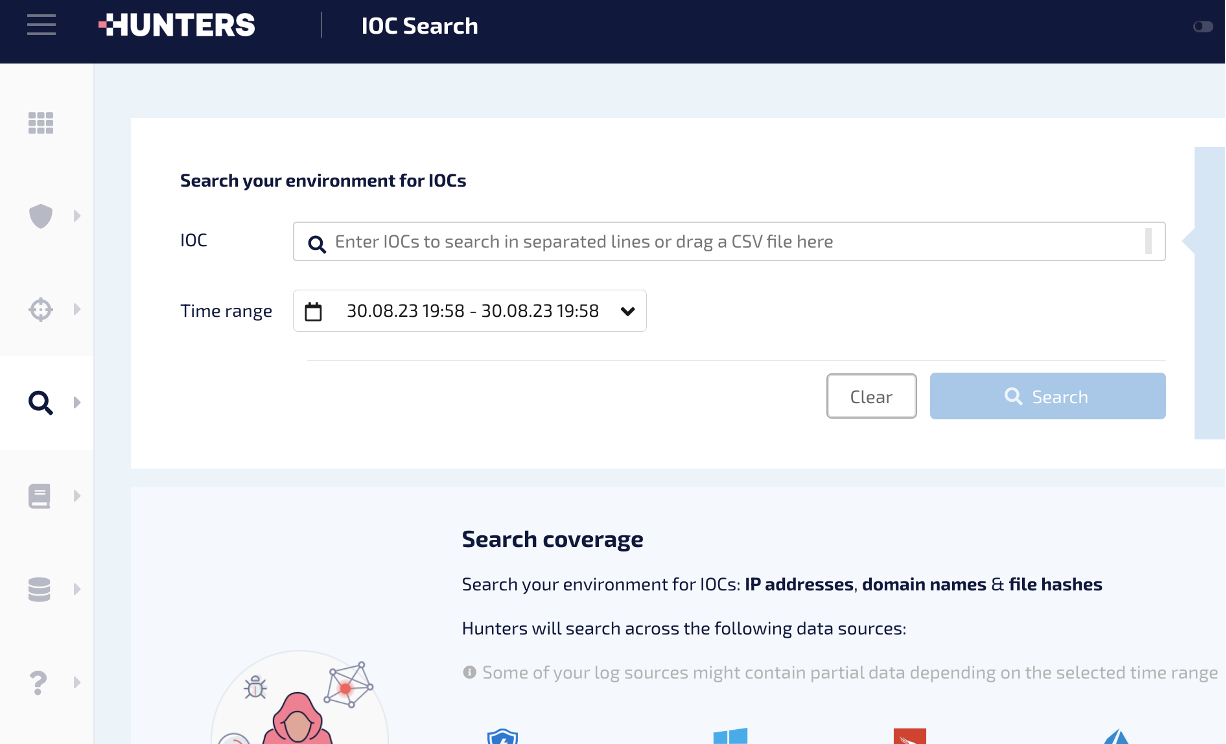
Hunters SOC Platform can replace your SIEM by delivering data ingestion, built-in and always up-to-date threat detection, and automated correlation and investigation to reduce risk, cost and complexity for SOC teams. Connect Hunters‘s unique detection capabilities with the CrowdStrike Falcon® platform‘s rich security data, such as running processes, network connections and file creations, and other data sources to attain full attack insight for faster response times.
- Detect logins to cloud applications
Analyze logins from a malicious IP address with SaaS application login logs to detect attacks on cloud applications - See full attack stories
Combine alerts on the same attack from different security tools for a full attack story without pivoting between tools - Identify unmanaged devices
Correlate CrowdStrike insights with SaaS and identity provider logs to identify devices without an Falcon agent installed
Get Started
Attain greater attack insight
- Detect logins to cloud applications
- See full attack stories
- Identify unmanaged devices
Not A CrowdStrike Customer?
Try CrowdStrikeSupport




